I’ve lost count of how many times friends have texted me some variation of: “Uh… I think my computer has been hacked?” Usually it’s accompanied by a blurry screenshot of a flashing red pop-up or a voicemail transcription that reads like a ransom note written by someone who failed English class twice. The panic is real, but the threats usually aren’t.
Scammers have gotten good — uncomfortably good. Their scripts are polished, their caller ID tricks are convincing, and their emails can look cleaner than half the corporate newsletters I get. But underneath the polish, the tactics haven’t changed much. In fact, most scams fall into just three buckets. If you can spot these patterns, you can shut down 90% of threats before they ever touch your bank account, inbox, or sanity.
Below, I’ll walk you through the Big Three Scams using scenarios that represent what millions of people encounter every day — no embellishment, no dramatization. The goal is simple: help you recognize the red flags before you click, share, or pay.
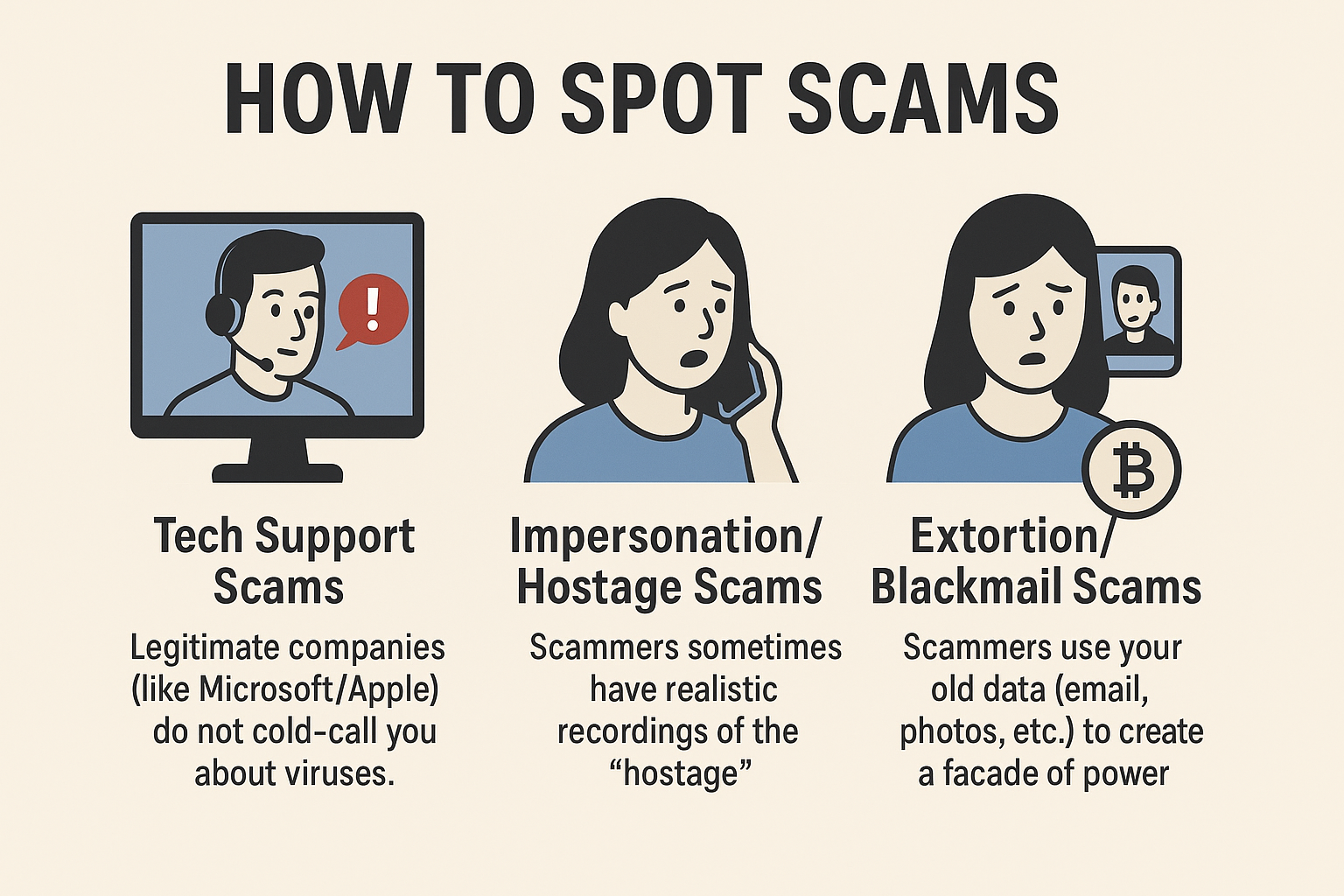
1. Tech Support Scams — “Microsoft Called Me” (No. They Didn’t.)
Tech support scams often start with an unexpected call claiming your computer is infected — a tactic designed to jolt you into compliance. The caller usually claims to represent Microsoft, Apple, or another well‑known company. They lean heavily on alarmist language, hoping you’ll panic before you pause to question the situation.
The Red Flags
- Unsolicited calls about viruses: Legitimate companies like Microsoft, Apple, Dell, or anyone else do not cold‑call strangers to notify them of malware.
- Demands for remote access: Scammers push for remote control because once inside, your files, passwords, and wallet are all fair game.
- Time pressure: They’ll insist the “infection” is spreading faster than gossip in a high‑school cafeteria.**: They’ll insist the “infection” is spreading faster than gossip in a high‑school cafeteria.
What This Means in the Real World
If you hand over remote access, you’re essentially giving a stranger the keys to your digital house and asking them to guard the fridge while you run errands. They will not guard the fridge.
What to Do Instead
Hang up. Open your computer normally. If you’re worried, run your own antivirus scan or visit the company’s real support page on your own terms.
2. Impersonation & Hostage Scams — Panic Is the Product
Impersonation and hostage-style scams typically arrive as urgent phone calls or voicemails claiming a loved one is in immediate danger. The details are vague, the emotion is high, and the goal is singular: push you into acting before verifying anything. Scammers know that if they can cloud your judgment for even 30 seconds, they can push you into acting before thinking.
The Red Flags
- Urgency on steroids: The “victim” is supposedly in extreme danger and you must act now.
- Requests to keep it secret: They don’t want you calling the supposedly endangered person.
- Voices that sound off: Often muffled, distorted, or drowned in background noise.
- Realistic voice recordings: Scammers sometimes use AI‑generated or stolen audio clips of the person they claim is in danger. The voice may sound eerily accurate, but it’s often stitched together or played out of context.
Here are a few specific examples of how these scams show up in the real world:
- A caller claims your sibling caused a car accident and is being held by the other driver until you pay for the damages.
- Someone pretends to be law enforcement and says your family member has been arrested and needs immediate bail money.
- A scammer says your child has been kidnapped, then plays a short audio clip that sounds like them crying — often pulled from social media or generated using AI.
- A caller pretends to be a hospital worker and claims your loved one is unconscious and needs emergency treatment, but they “can’t release information” until you pay a fee.
Why This Works
When fear hits, your brain does what mine does when I smell fresh cinnamon rolls: it shuts down rational thought. Scammers rely on that moment of emotional hijack.
What to Do Instead
Hang up. Contact the person directly. If they don’t respond, call another family member or friend. The moment you independently confirm safety, the scam collapses like a cheap camping chair.
3. Extortion & Blackmail Scams — The Bitcoin Ultimatum
Extortion and blackmail scams usually start with an email claiming the scammer has compromising information about you. As proof, the scammer often reveals some personal information about you or your family. However, these scams usually rely on information pulled from old data breaches or publicly available information. They might use your email address from a long‑ago data breach, a photo of your home pulled from Google Maps, or even information from a forgotten social media profile. The scammer frames this as “proof” of deeper access or more damaging material, even though the data is almost always publicly available.
The Red Flags
- Claims of having “secret” evidence: But the evidence is often something anyone could find with a quick Google search.
- Bitcoin payment demands: Scammers love crypto because it’s harder to trace.
- Generic language: If they really had dirt, they’d be specific.
What This Means in Real Life
These emails are mass‑mailed scare bombs. Scammers fire them out like confetti, hoping one lands on someone already feeling vulnerable.
What to Do Instead
Before ignoring a threat email, check whether your information has appeared in a known data breach. A trusted resource like Have I Been Pwned can help you verify if your email or passwords were exposed in past breaches; if they were, it doesn’t mean the scam is real — only that the scammer may be pulling old data to intimidate you.
If the “evidence” was public or from a known breach, ignore the message. Block the sender. And if anything seems genuinely concerning, talk to someone you trust before acting.
How to Report Scams — Turn the Tables
The good news? You don’t have to just hang up and mutter, “Well, that was annoying.” Reporting scams actually helps put the brakes on these crooks. In the U.S., you can send tips about phone, email, or online scams to the Federal Trade Commission (FTC) at reportfraud.ftc.gov, or to the Internet Crime Complaint Center (IC3) at www.ic3.gov for internet-based shenanigans.
If someone is impersonating a loved one, making threats, or demanding money, a quick call to local law enforcement doesn’t hurt either and you can report them to CISA or the FBI. Outside the U.S.? Check your country’s consumer protection or cybercrime authority. Even if the scammer got nothing from you, reporting them is like sprinkling digital pepper spray—they can’t hurt anyone else if authorities know where to find them.
Final Thoughts — Awareness Is Armor
Scams evolve, but the psychology behind them is practically prehistoric. Fear. Urgency. Authority. These are the tools scammers lean on because they work.
But once you see the patterns, the power shifts. You stop reacting on instinct and start responding with skepticism. And that’s the real goal: not to turn you into a cybersecurity expert, but to build a kind of street smarts for the digital world.
If you remember just one thing from this guide, make it this: anyone trying to make you act before you think is not on your side.
Stay suspicious, stay steady, and stay in control.